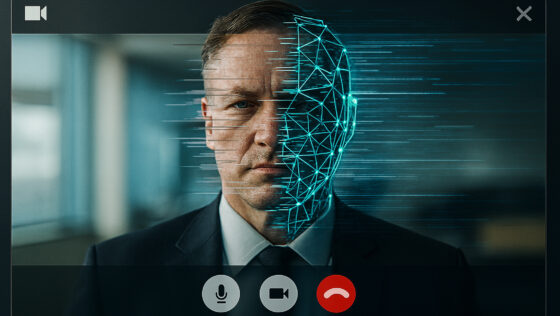
Is MFA No Longer Enough?
Multi-factor authentication is a powerful thing. It’s easy to set up, works well at all levels, and the main downside for most people is screaming at your phone that no, you don’t have access to the email account you set … Read More