Multi-factor authentication is a powerful thing. It’s easy to set up, works well at all levels, and the main downside for most people is screaming at your phone that no, you don’t have access to the email account you set up in 2007. MFA can block more than 99% of identity-based attacks. But it’s not perfect.
More and more, we’re seeing attackers finding ways to bypass MFA and access critical systems and data. In this post, we’ll break down what’s happening and show you what you can do to stay safe.
Types of MFA bypass attacks
Initial access attacks, according to a CrowdStrike report, accounted for 52% of vulnerabilities in 2024, and 79% of these were malware-free. This suggests that attackers are using bypass tactics rather than traditional methods.
So what are they doing? There are a few different ways in which attackers try to bypass MFA. Let’s take a quick look at the most common.
Token theft was used in 31% of attacks in a 2025 Verizon report. This type of attack involves stealing authentication tokens after a user completes MFA. Attackers use methods like malware and phishing to get these tokens, and can then access the account even after the owner resets passwords.
Prompt bombing, also known as MFA fatigue attacks, was found in 14% of all social engineering incidents in another Verizon report. This is where attackers obtain some of a user’s login credentials and then repeatedly spam the account with login requests. The aim is to confuse or trick the user into granting access.
Session hijacking involves capturing active session cookies or tokens from a post-MFA browser session and then replaying them from a different device, essentially impersonating the legitimate user. These tokens “prove” authentication, so the attacker doesn’t have to go through MFA.
Adversary-in-the-Middle (AiTM) is where attackers set up a phishing proxy between the user and the service. The user then unknowingly enters their login details and approves MFA on this fake page, which captures the session token and allows the attacker to gain access.
SIM swapping involves tricking mobile carriers into porting another person’s phone number to their SIM. This allows them to intercept MFA codes via SMS and gain access to the victim’s accounts.
How to defend against MFA bypass attacks
As you can see, there are a few different angles to worry about here. But there are plenty of steps you can take to protect your assets and employees against MFA bypass attacks.
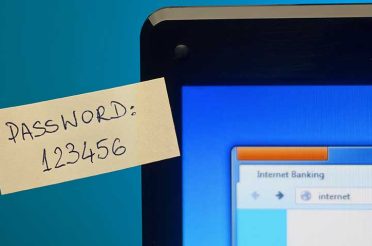
● Strengthen your authentication controls, for example, by using phishing-resistant MFA methods like FIDO2 hardware keys or biometrics
● Set up conditional access policies that look at device compliance, location, and network risk in addition to MFA
● Use strong password policies or passwordless authentication
● Monitor sessions for any red flags like new devices, bulk data downloads, or OAuth app authorisations
● Make an inventory of all apps that use OAuth tokens and revoke any unused or high-risk ones. These tokens bypass MFA by design, which makes them a major risk.
On top of these technical steps, you’ll also want to educate your employees and help them prepare for incidents.
Make sure your teams can recognise phishing and social engineering tactics that target MFA credentials like AiTM attacks. And set up a well-defined incident response plan for when things go wrong, so you can quickly revoke tokens and investigate any issues.
It’s always best to work with a team of experts. Here at Aryon, we can assist you in managing your cybersecurity, including MFA defence, so you can focus on what you do best.
Book a call with us to find out more and get started.