Cybersecurity is critical for organisations and the importance of it cannot be understated, as the consequences of a security breach can be disastrous. The rate and complexity of cyberattacks continues to increase, and ongoing resistance is required to safeguard private information.
During 2022, Internet of Things malware attacks increased by 87%, and with the rise of AI tools such as Chat GPT, this danger will continue to grow. Therefore, it is essential that organisations maintain a proactive approach to their cybersecurity.
One approach to security that is recommended is the Secure-by-Design concept, and it is an approach that the cybersecurity agencies of the Five Eyes alliance, which includes Australia, are now advocating.
This collaborative effort highlights the importance of global cybersecurity, and its promotion is an acknowledgement that a coordinated effort is needed to combat digital dangers.
In this article we explain what Secure-by-Design is, along with its importance and the benefits that are gained by embracing it, and how your organisation can implement it and incorporate its principles.
What Is Secure-By-Design?
Secure-by-Design is a proactive, security orientated approach to digital products and services, which are designed to align with an organisation’s own cybersecurity goals.
It requires threats to security to be considered from the outset of creation of a product or service, and it promotes heightened security measures throughout the entire design and delivery process. Its basic tenet is to protect data and privacy through improved design, implementation, and delivery, and ultimately, assist digital products and services to exist with fewer, if any, security vulnerabilities.
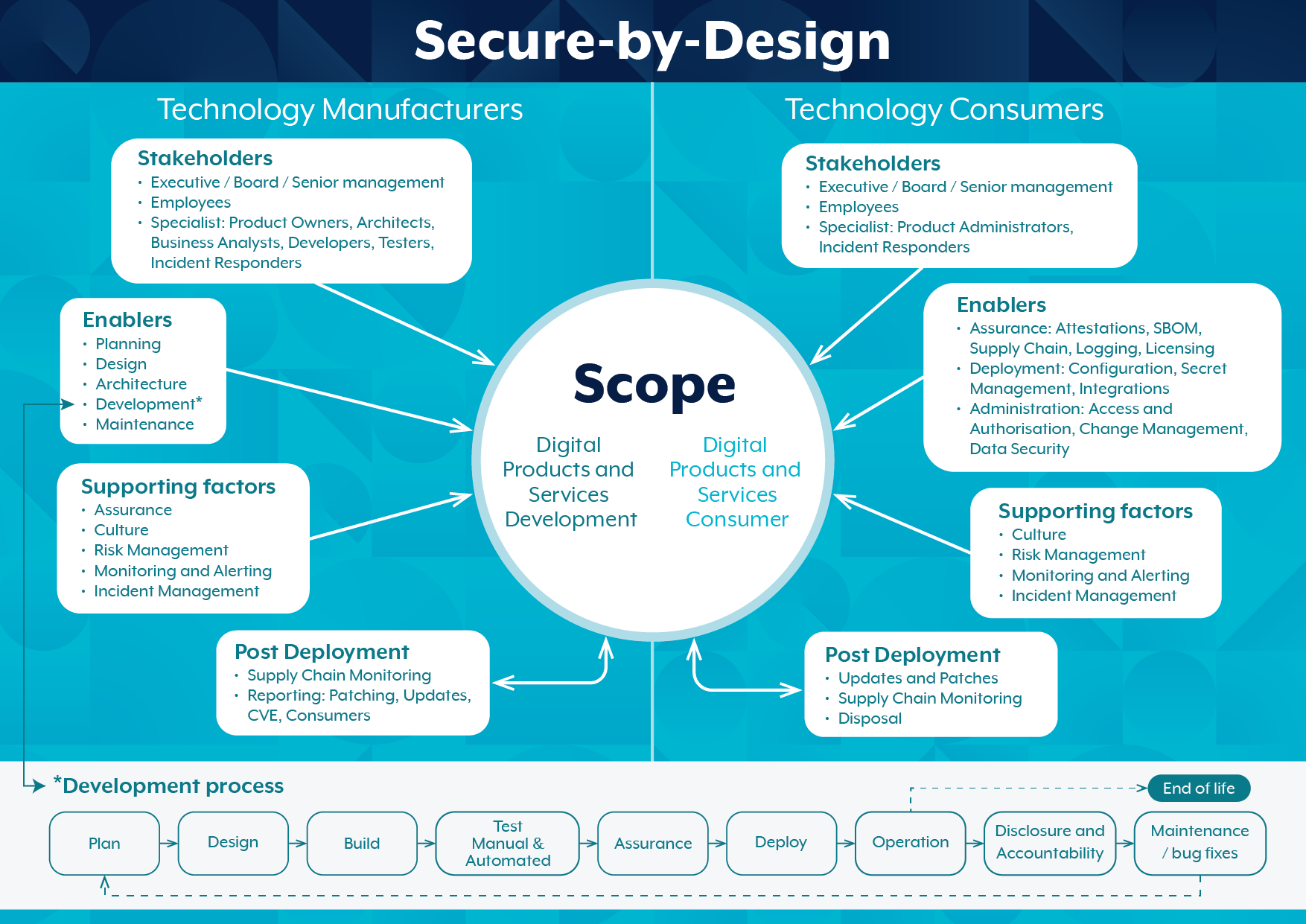
The Australian Cyber Security Centre, which falls under the remit of the Australian Signals Directorate, has released an infographic which illustrates what Secure-by-Design is, along with its associated stakeholders, enablers, and the digital eco-system which it exists in:
The Importance Of Secure-By-Design
With the whole world coming online, private and critical data is increasingly being attached to digital products and services, and if that data is comprised, there can be negative economic, privacy, and reputational damage to organisations and individuals.
Australian citizens are increasingly being exposed to, and impacted by, data breaches and cybercrimes, which mostly have been instigated through vulnerabilities in digital products and services.
The governments of the world recognise this, and they are attempting to address it by advocating for the Secure-by-Design approach, and the encouragement of manufactures of technology to play a role in increasing cybersecurity.
Now more than ever, it is crucial for technology manufacturers to ensure the security of their digital products and services through a security-first approach, and it is expected that consumers should receive digital products and services that are secure and free from cyber vulnerabilities.
The Key Aspects Of Secure-By-Design
The key aspects of Secure-by-Design include:
Risk Assessment: Identifying any risks and vulnerabilities during the design and delivery process.
Maintaining A Standard Security Framework: The application of consistent standards of security by following an established framework or procedures.
Controlled Privileges: A limit of access to resources to only those who need it.
Depth Of Defence: Implementing multiple layers of security throughout systems.
Regular Updating: The regular updating of security measures to ensure that they address all threats.
Consumer Education: The education of consumers regarding security best practices as well as potential risks.
The Benefits Of Secure-By-Design
The benefits or Secure-by-Design are many, and they include:
A Proactive Security Posture
Traditionally cybersecurity approaches are reactive, which means that security issues are only addressed after an incident has occurred. By nature, Secure-by-Design implements security measures from the beginning, which minimises vulnerabilities from the outset.
Cost Savings
Rectifying security issues after a product or service has been produced and delivered is costly, and by addressing improvements from the start, money can be saved, and issues can be prevented from occurring in the first place.
Regulatory Compliance
Data and its protection are subject to strict regulatory conditions imposed by the Australian and international governments. Secure-by-Design acknowledges these and can help an organisation to be regulatory compliant and avoid costly fines and penalties from non-compliance.
Reputation Management
Should a security breach occur, everyone involved will be held accountable and suffer the consequences. Secure-by-Design can assist organisations avoid this undesirable outcome, while also enhancing corporate and client reputation.
Future-Proofing
As cyberthreats will continue to be a major issue and evolve, Secure-by-Design can offer a degree of future-proofing against threats, through the establishment of a strong security foundation.
A Minimisation Of Attack Surfaces
By nature, Secure-by-Design reduces the amount of attack surfaces that are available to cybercriminals, which will increase an organisations security posture, and diminish the opportunity for a breach.
How Can Organisations Implement Secure-by-Design?
Organisations can implement the principles of Secure-by-Design in a number of ways, including:
- When purchasing digital products, such as hardware or software, enquire if Secure-by-Design principles were used in their creation, or through the supply process
- Incorporate Secure-by-Design principles into their own activities, such as when undertaking an infrastructure upgrade or creating a product or service.
Secure-By-Design: Its Importance And Its Implementation
The Secure-by-Design concept is a recommended security strategy for those that are involved in producing or receiving digital products and services, and the fact that major world governments, including Australia, are now firmly promoting it, is further proof of its value, for producers and consumers alike.
For more information about Secure-by-Design or any other cybersecurity concerns, please contact us today, so that we can best assist you.







