Cybersecurity threats are on the rise. Global security incidents increased 70% between February and March 2024. To stay ahead of these threats, organisations of all sizes need a planned approach to addressing cybersecurity challenges.
Enter the National Institute of Standards and Technology (NIST) which haswhich created thea Cybersecurity Framework (CSF). This industry-agnostic framework empowers companies to manage and decrease cybersecurity risks. Updated in 2024 to NIST CSF 2.0, it provides an efficient and flexible approach for organisations of all sizes. This guide simplifies the framework, making it more accessible for everyone.
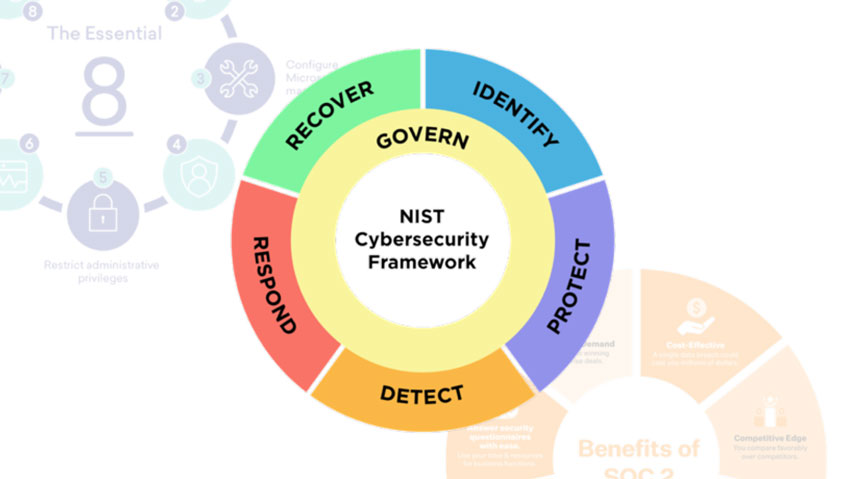
Understanding NIST CSF 2.0
The basis of CSF 2.0 lies in its five Core Functions: Identify, Protect, Detect, Respond, and Recover, which provide an elevated view of cybersecurity risk and how organisations manage it. This allows for an active approach to tackling threats.
Let’s break down the Core Functions of NIST CSF 2.0:
- Identify: This involves pinpointing your organisation’s assets, cyber risks, and vulnerabilities. You can’t protect what you don’t understand. Knowledge of what needs protection is crucial before applying safeguards.
- Protect: Here, the focus is on implementing safeguards to deter, detect, and reduce cybersecurity risks. Think firewalls, detection systems, and encryption of data.
- Detect: Early detection of incidents minimises damage. This function emphasises the need to have mechanisms in place to recognise and report suspicious activity.
- Respond: This empowers you to take decisive action, i and includinges activities such as containing the threat, eradication, recovery, and learning.
- Recover: Taking charge of restoring operations after an incident, including data restoration, system recovery, and implementing continuity plans.
Customise Your Cybersecurity Approach with Profiles and Tiers
The new framework introduces Profiles and Tiers to help organisations adapt their cybersecurity practices to their needs, risks, and resources.
- Profiles: Represent the orientation of the Functions, Categories, and Subcategories in line with your organisational requirements, tolerance of risk, and resources.
- Tiers: Provide context on how your organisation views and manages cybersecurity risk. They range from Partial, known as Tier 1, to Adaptive, known as Tier 4.
Boost Your Cybersecurity with the Advantages of NIST CSF 2.0
Implementing NIST CSF 2.0 offers several advantages:
- Improved Cybersecurity Posture: By following the framework’s guidance, organisations can develop a more comprehensive and effective cybersecurity program.
- Reduced Risk of Cyberattacks: The framework helps identify and mitigate cybersecurity risks, lowering the likelihood of cyberattacks.
- Enhanced Compliance: NIST CSF 2.0 aligns with many industry standards and regulations, aiding compliance efforts.
- Improved Communication: The framework provides a common language for discussing cybersecurity risks, fostering better communication within your organisation.
- Cost Savings: By preventing cyberattacks and reducing the impact of incidents, NIST CSF 2.0 can help organisations save money.
Start Your NIST CSF 2.0 Journey
Ready to leverage NIST CSF 2.0? Here’s how to get started:
- Familiarise Yourself: Take time to read through the NIST CSF 2.0 publication and understand the Core Functions and categories.
- Assess Your Current State: Assess your current cybersecurity posture to identify any gaps or weaknesses.
- Develop a Plan: Based on your assessment, develop a cybersecurity plan that outlines how you’ll implement the NIST CSF 2.0 framework in your organisation.
- Seek Professional Help: Need guidance and support getting started? Consider partnering with a specialised network and security services provider such as Aryon.
By following these steps, you can begin deploying NIST CSF 2.0 while simultaneously improving your organisation’s cybersecurity posture.
Identify Your Risks: Schedule a Cybersecurity Assessment Today